Auth⚓︎
Auth⚓︎
Auth?
Auth points to Authentication and Authorization. They come from REST API communication.
- Without Authentication → 401 (Do not know who you are).
- Without Authorization → 403 (Do not have permission to access resources).
Token⚓︎
To realize the two Auth principles. Including Token becomes essential.
Why Token?
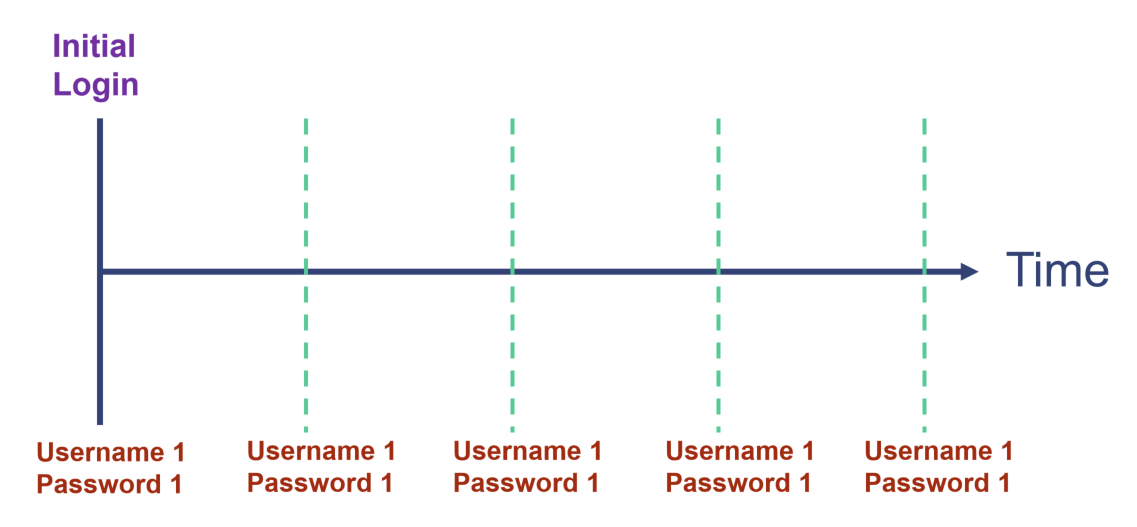
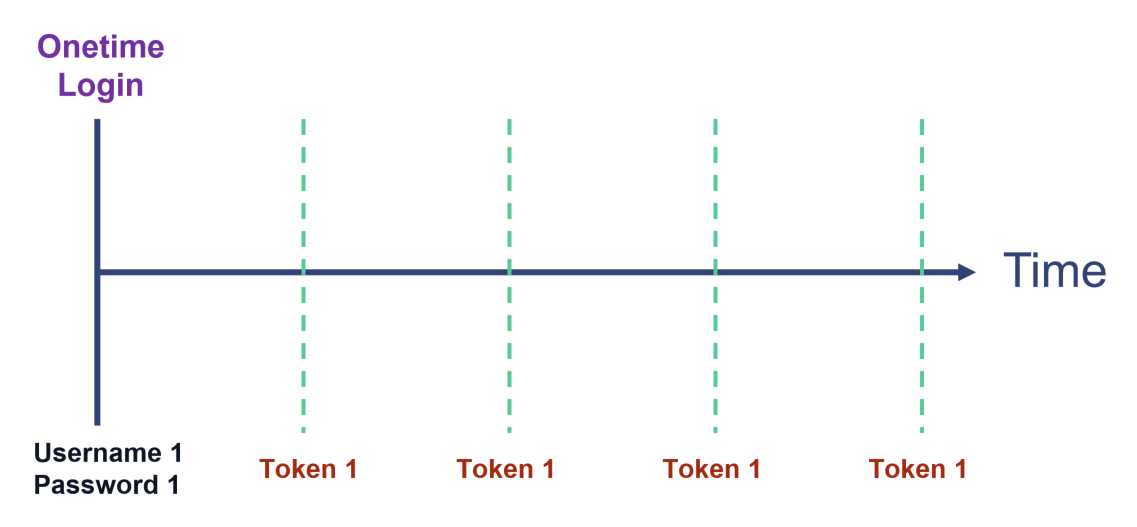
Compared with username & password, tokens are temporary, stored in browser or device. When sessions complete or exceed the expiration time, not like username & password, they are automatically destroyed.
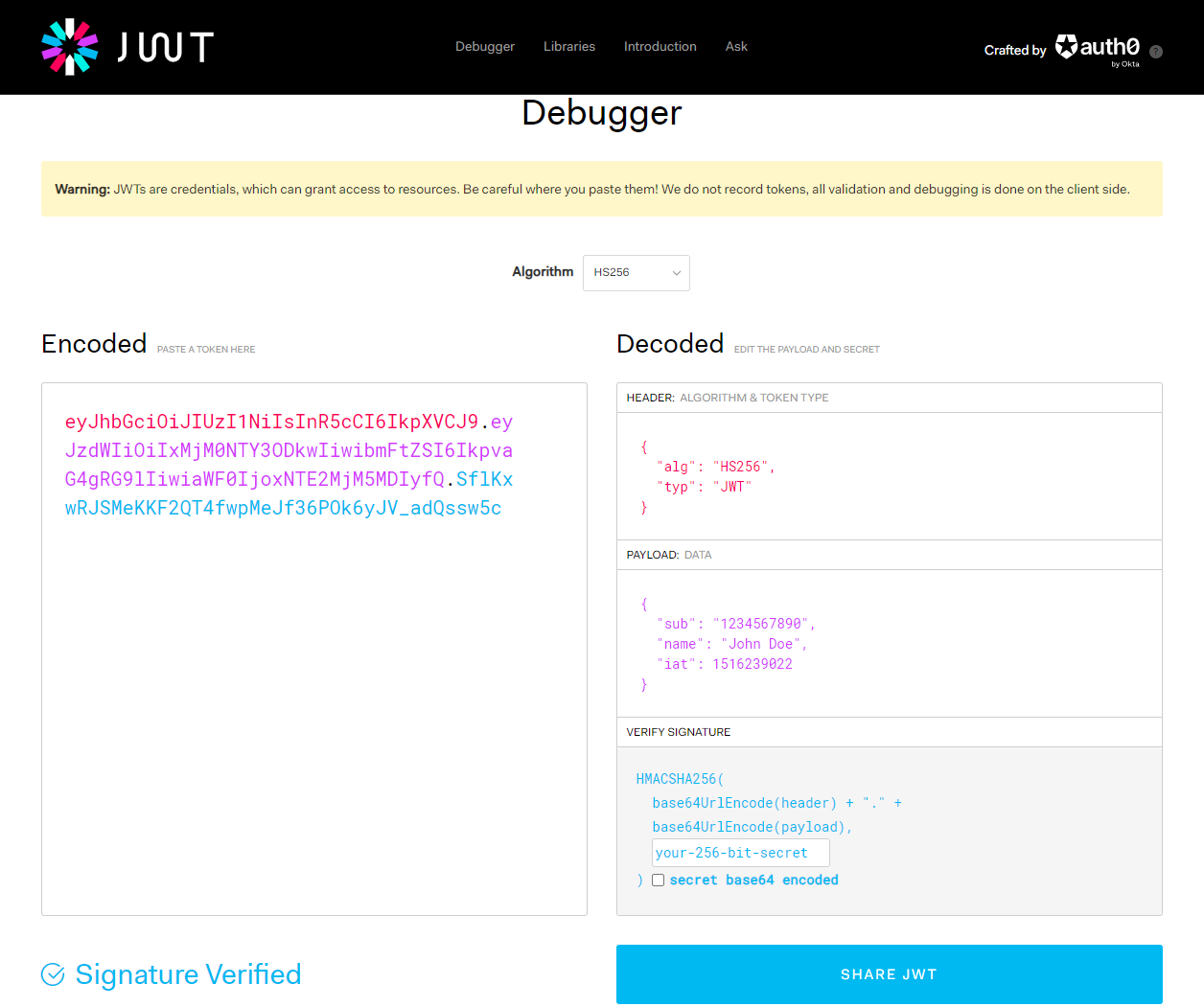
JWT.io⚓︎
JWT.io for Token generation
JWT.io is constructed by below components:
- Header: Identify:
- Which algorithm(normally HS256) to generate the signature.
- What token type (Here JWT).
- Payload: A set of claims.
- Signature: Securely validates the token, calculated by encoding the header and payload using
Base64URL Encoding [RFC 7519](https://www.rfc-editor.org/rfc/rfc7519)
How to use Token⚓︎
How to apply Token?
We inject tokens in the HTTP header.
OAuth 2.0⚓︎
Why need two Tokens?
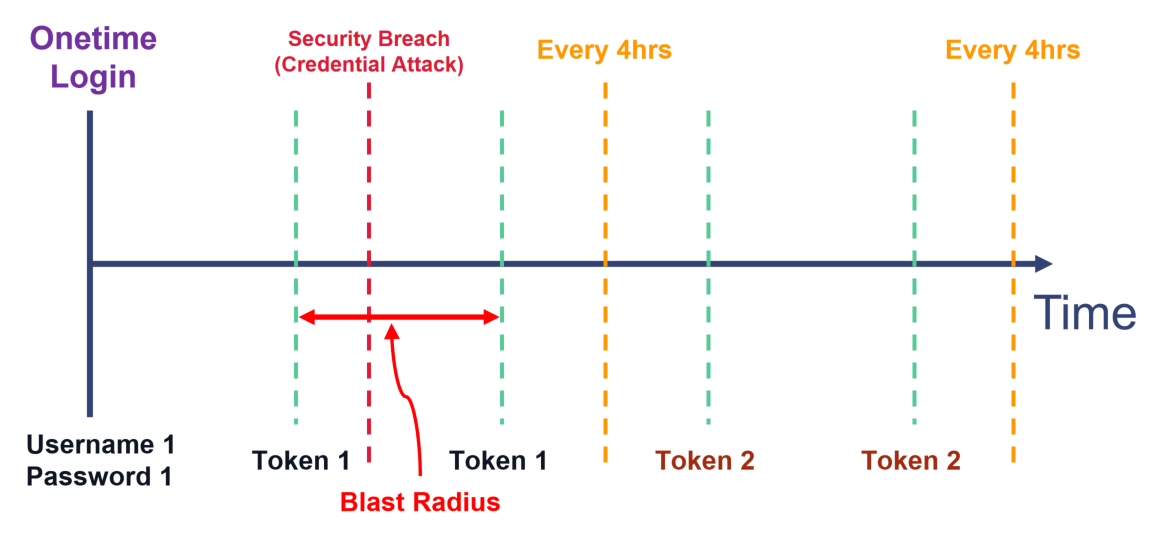
It limits the blast radius of a credential attack.
Credential attack!
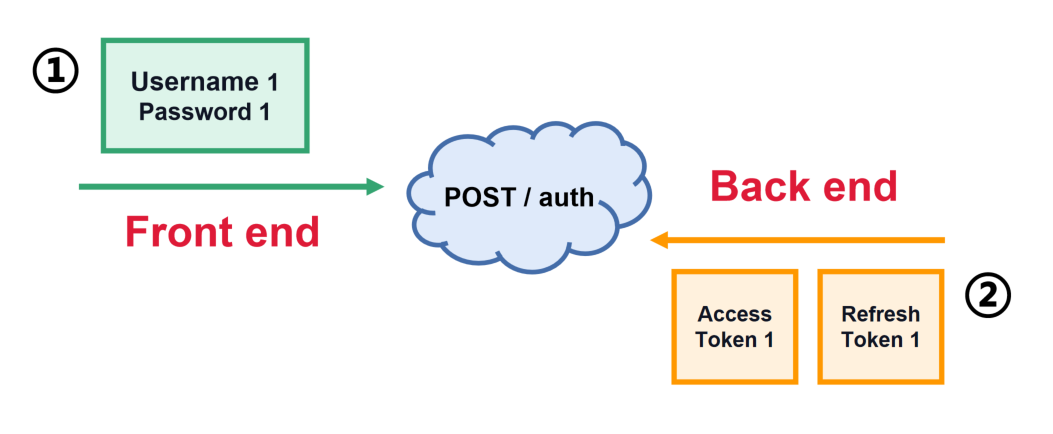
Username-Password Auth
One Token Auth
Two Token Auth (OAuth 2.0)
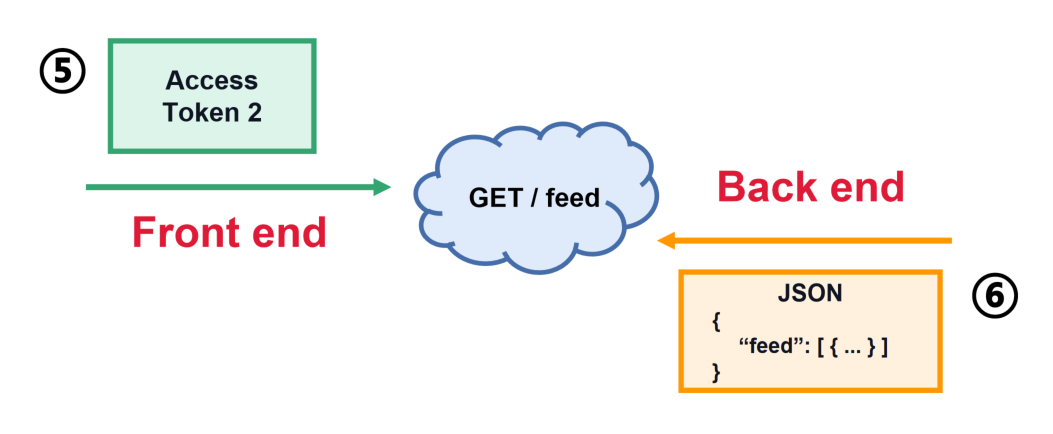
Implement OAuth 2.0⚓︎
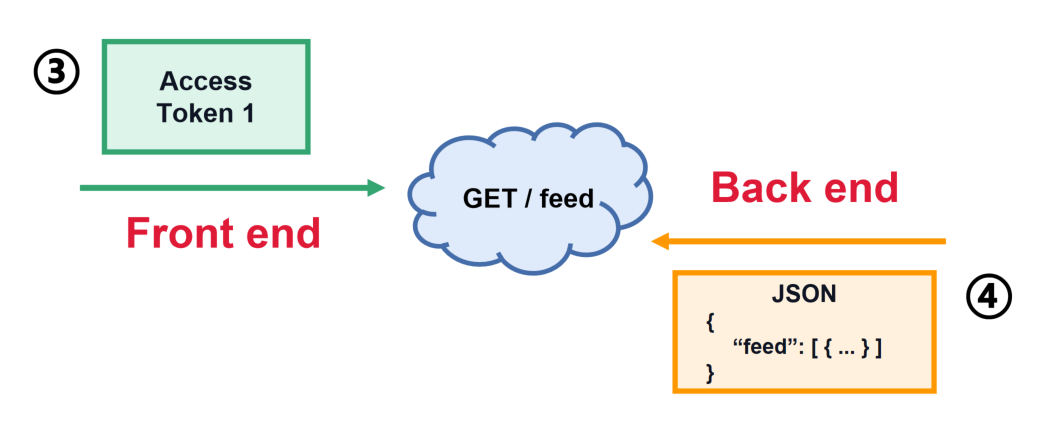
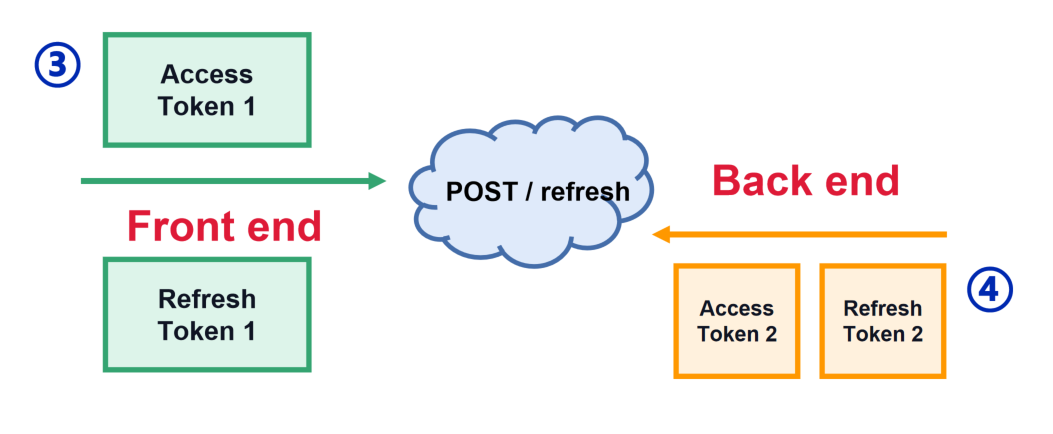
For the two tokens, one is named Access Token; another is named Refresh Token.
Difference between the two tokens?
-
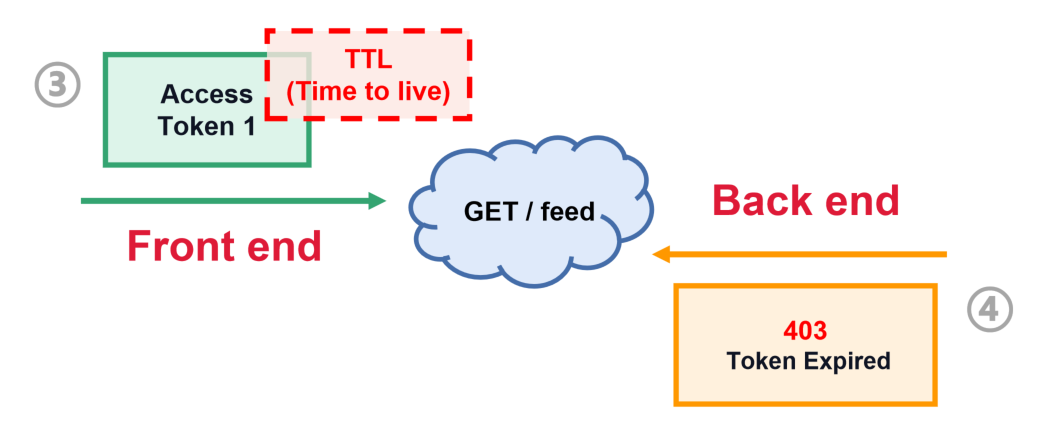
Access tokenhave"Time-to-live", which is the maximum that the access token will be valid for use within the application. -
Refresh tokenshave longer expiration times than access tokens. The exsistance ofrefresh tokensallows you to use shorter lifetimes for access tokens WITHOUT having to request user credentials multiple times.
Iterations Diagram